Wish you all the greetings of “Subho Bijoya”.
May Goddess Durga brings best of health, happiness, peace & prosperity to you, your family and loved ones.
As Maa Durga Departs for her Home, May she leave behind her blessings & love to fill your heart and home with happiness & sweet moments. Lets start a great life by conquering our eternal evils.
Lets take the oath to give a dimension to our life on this auspicious festival. With plenty of peace and prosperity, may Maa bless you with happiness all the year through!
With the end of long desired break for a week during Durgapuja Festival, it is high time for all of us to think, strategies, consolidate and optimize our organization infrastructure.
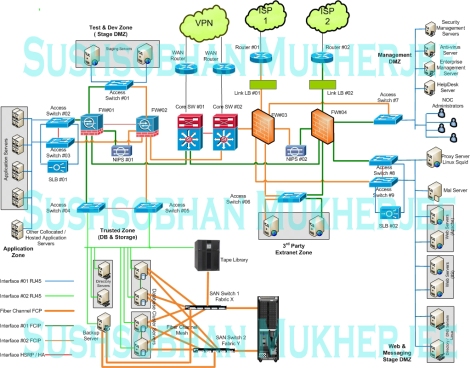
An enterprise typically is having heterogeneous environment where business is in need of different elements like Internet Bandwidth, Router, Switches, Firewall /UTM, Load Balancer, Servers, Storage, Backup, Desktop, Operating Systems, Database, Applications, Virtualizations, End Points, Wifi, CCTV/IP Camera Based Surveillance, Biometric Attendance, RF ID based Access Control and so on. In addition to this there is a huge Non-IT infrastructure needs to support these IT infra like UPS, DG Set, Building Management System, Cooling Systems (PAC, CAC), Civil, Interior etc.
One sample architecture is attached below to make all of you understand how critical it can be.
But how an Enterprise / Organization invest on these aspects? Is it possible for the IT administrator/Systems Incharge to handle such a wide spectrum of systems with his own domain knowledge, evaluate, finalize and implement as per organization objective?
Answer is “No”.
Then how it happens? It happens by “Assumptions” and OEM/SI “Influence”.
There are wide variety of OEMs in almost all variants. Few of the examples are as follows:
- Internet Bandwidth: TATA, Jio, Airtel, Sify, Vodafone and so on,
- Computing: HP, Dell, IBM, Fujitsu, Lenovo, Acer, ASUS and so on,
- Routing/ Switching: Cisco, HP, Juniper, Brocade, Avaya, Allied Telesis, Dlink, Extreme, Digisol, Netgear and so on,
- Security: PaloAlto, Fortinet, Cisco, Juniper, Sophos, Sonicwall, Symantec, Kaspersky, Trend Micro, FireEye and so on,
- Virtualization: VMware, Citrix, Microsoft, Ncomputing, VXL, Enjay and so on,
- Wireless: Ruckus, Motorola, Cisco, Aruba, Ubiquity, Engenius, Digisol, Ubiquiti, Netgear, Dlink, Alcon and so on.
- Gateway: 24 Online, Nomadix, Ucopia, Peplink, Radware, Bluecoat, Allot, F5, Citrix and so on
- Surveillance: Sony Ipela, Samsung, LG, Tyco, Bosch, Honeywell, Pelco, Zicom, Alcon, CP Plus, Sparsh, Hikvision, Digisol and so on.
- Video Conferencing: Polycom, Huawei, Cisco, VU, Avaya and so on.
- Networking: Schneider Electric, Tyco, R&M, Systimax, Siemon, Molex, DAX, Dlink and so on.
- Software: Microsoft, Redhat, Novell, CA, IBM, HP and so on.
- UPS : Eton, APC, Emerson, Delta etc
- PAC : Emerson
- DG : Kirlosker, Jakson etc
Now it is literally impossible for an individual to avoid influence from almost all the above. Everyone pitches it’s superiority compared to the other and intends to prove the other one does not suit the customer requirement.
There was a situation of a customer where they had best of the bread products in almost all layers, but still they had application access issues (SAP with Oracle Database) through its blade server. They used to restart the gateway UTM, remove cables from the server etc. kind of short term break fixes instead of identifying the real root cause. The moment they spelled out to their existing service providers, all different stake holders were prone to sell their products. Internet service provider wanted to upgrade the bandwidth since the issue was due to over utilization of the bandwidth as per them. The UTM supplier and OEM wanted to sell the higher Box through Buyback since it apparently got over utilized as per their observations. Similarly LAN vendor wanted to change the entire cabling from Cat5 to Cat 6 to improve performance. And off course customer was literally confused. Finally the troubleshooting revealed the configuration issues of their existing resources. On configuration of VLAN and deployment of the core switch in L3 mode with inter VLAN routing sorted out the problem. The problem was the generation of malicious traffic from the LAN machines which were part of same broadcast domain with the servers. Moreover, it has also been found the kind of resources they had in terms of the infra was surplus and would suffice their future needs at least for three years.
This is not uncommon in nature. Generally this is the pattern where market is inclined to sell more and more products/ services of theirs instead of doing due diligence to actual needs.
Let me give you one more example. One of the leading hospitality customer was having wifi implemented in the property from one of the leading renowned brand. The property had 67 no.s of access points installed in total 7 floors. The product was leader in the segment. But still customer was having lot of Wifi related issues with specifically apple devices. The moment they approached the provider, they suggested to have 20 more access points! Adding more and more devices can never solve the problem (moreover only problem in Apple devices cannot be a wifi coverage issue, it is bound to be a configuration issue). Wifi deployment needs proper survey and deployment plan as per needs not just deploying devices here and there. Additionally they bought the devices for some extraordinary features (which are true), but none of those were being used by them (as was not required for them). Later on they procured low cost devices (one fifth of the cost of existing devices) and their purpose was served with satisfaction.
Hence the idea should be to have a stock of the existing infra, understand it’s utilization, configuration and organization objective in order to select a product / solution. It is not only about selection of a product as per need, but also it is important to configure/customize as per organization business need in order to synchronize with the objective and have fruitful result.
With the blessings of Goddess Durga, it is high time for all of us to go back, understand the situation of our existing infrastructure before we invest further in products. Also let us enlighten ourselves to choose a right product, evaluate as per needs, not just by name.
Evaluation of existing infrastructure (which is already built and running) is not possible manually in case proper process are not in place. This is done by deployment of some automated tools which generate several logs and consultants manually correlate the logs and assist organizations with report on GAP Analysis and Remediation Plans.
Any queries from the interested readers, we will be happy to address.